
Hacking Articles on Twitter: "Common Ports Cheat Sheet https://t.co/62PMMHvy3o #infosec #cybersecurity #cybersecuritytips # pentesting #oscp #redteam #informationsecurity #cissp #CyberSec #networking #networksecurity #CheatSheet #infosecurity ...

Ports1.pdf - Pentest Book Ports General AIO Penetration Testing Methodology - 0DAYsecurity.com Port 21 - FTP nmap -script | Course Hero
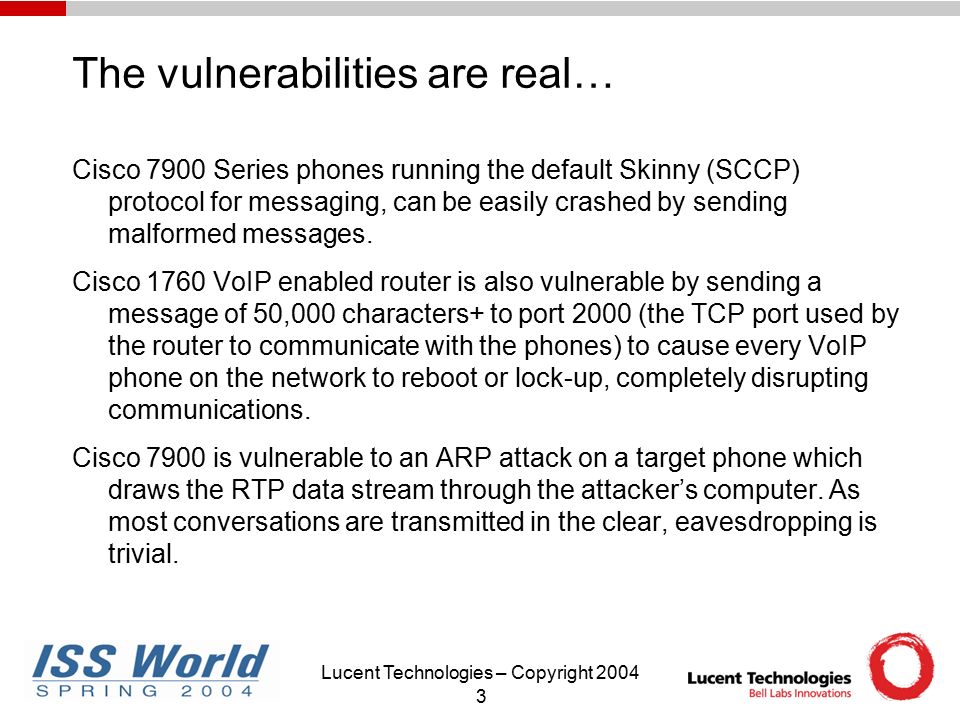
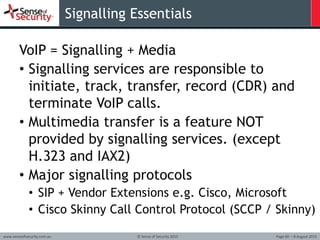
Track A: Network Security 9AM-10AM May 6, 2004 Security And Next Generation VoIP George G. McBride Senior Manager, Security Practice Lucent Technologies. - ppt download
Python-Penetration-Testing-Essentials-Second-Edition/port.txt at master · PacktPublishing/Python-Penetration-Testing-Essentials-Second-Edition · GitHub

Interview #common #questions TCP/UDP port numbers. For cyber security professionals you can also think about the payloads you can use if these ports are open. #indincybersecuritysolutions #cybersecurity... - Indian Cyber Security Solutions -

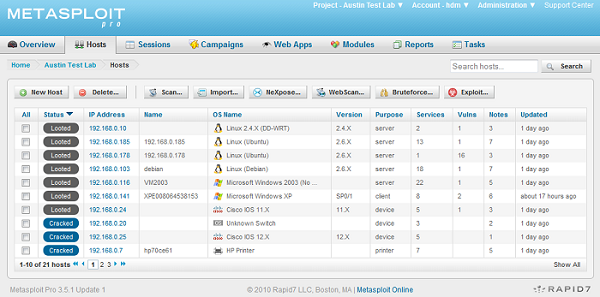

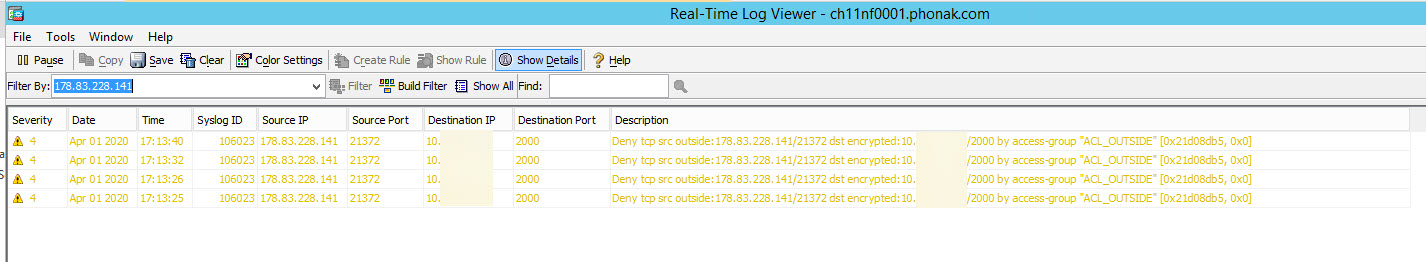
![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://hub.packtpub.com/wp-content/uploads/2018/06/DoS-attacks.jpg)

![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/5e8d8982-3c95-48ca-bae9-9656fa4bfaa2.png)
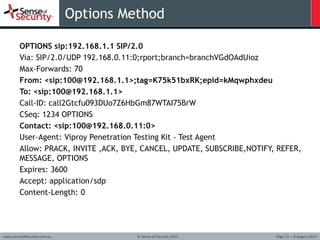

![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/66d14bd4-3ddf-49ad-98cc-066b155b160f.png)



![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/d2578ffa-594d-4f53-acf3-49746685408f.png)

